Modernizing a legacy system does not always mean throwing it away entirely. It can mean incrementally adapting it to the present
What is a legacy System
A legacy system is outdated computing hardware or software that continues to run critical operations even though it is no longer actively supported or updated. These include old mainframes, specialised terminals, on-premises enterprise software (such as ERP or CRM tools built for Windows XP-era servers), and applications written in decades-old languages like COBOL or Visual Basic 6.

A legacy system is not merely “old” technology. It is one that still fulfils its original purpose but cannot grow, integrate, or adapt: no vendor support, no security patches, and increasingly rare expertise to maintain it.
By definition, it typically no longer receives updates or vendor support, may rely on obsolete file formats or hardware, and often requires rare expertise to maintain. The outcome is a system that runs the business the same way it always has, yet cannot easily incorporate new features, adapt to current security standards, or communicate with newer technology.
Why So Many Organisations Still Cling to Legacy Systems
Many organisations know their systems are outdated. Retirement, however, is another matter entirely.
The most fundamental reason is pragmatic: legacy systems still work, for now. If a banking backend keeps processing transactions or a manufacturing system keeps running production orders without fault, decision-makers default to “if it isn’t broken, don’t fix it.” Replacing decades of embedded business logic demands enormous upfront investment in time, money, and retraining, costs that are easy to defer when the lights are still on.
Over years and decades, complex requirements and compliance rules become baked into legacy code. As one fintech expert observes, banks have invested so heavily in mainframes and COBOL that their systems have grown “so intricate that no one fully understands them anymore.” A complete rewrite means navigating uncharted territory, with no guarantee that every hidden rule and edge case survives the migration.
Regulated industries are especially prone to this attachment.

In banking, core transaction processing and compliance frameworks were built around legacy platforms long before modern infrastructure existed. Regulators trust their mature audit trails. Millions of transactions run through these systems every day. For many banks, the legacy platform is not just old technology; it is an embedded part of how they meet regulatory obligations and operate reliably.
Until a credible, tested alternative exists, continuing to use the legacy system feels like the safer, if temporary, choice.
Internet Explorer: A Legacy System Case Study
Microsoft’s Internet Explorer illustrates precisely how a widely used product becomes a legacy system, not because it stops working, but because support ends and the world moves on.
On June 15, 2022, Microsoft officially retired Internet Explorer 11 for most Windows 10 users, ending all security updates and technical support. Support for IE 10 and earlier had already ended in January 2020. Microsoft Edge became the official successor, with a built-in IE Mode designed for organisations that still need to access older internal sites. Microsoft has committed to supporting IE Mode in Edge until at least 2029, with one year’s notice before discontinuation.
What this example demonstrates is worth sitting with. Internet Explorer did not stop loading pages on June 15, 2022. It simply stopped receiving fixes. Any security flaw discovered after that date will never be patched, leaving organisations still running it permanently exposed.
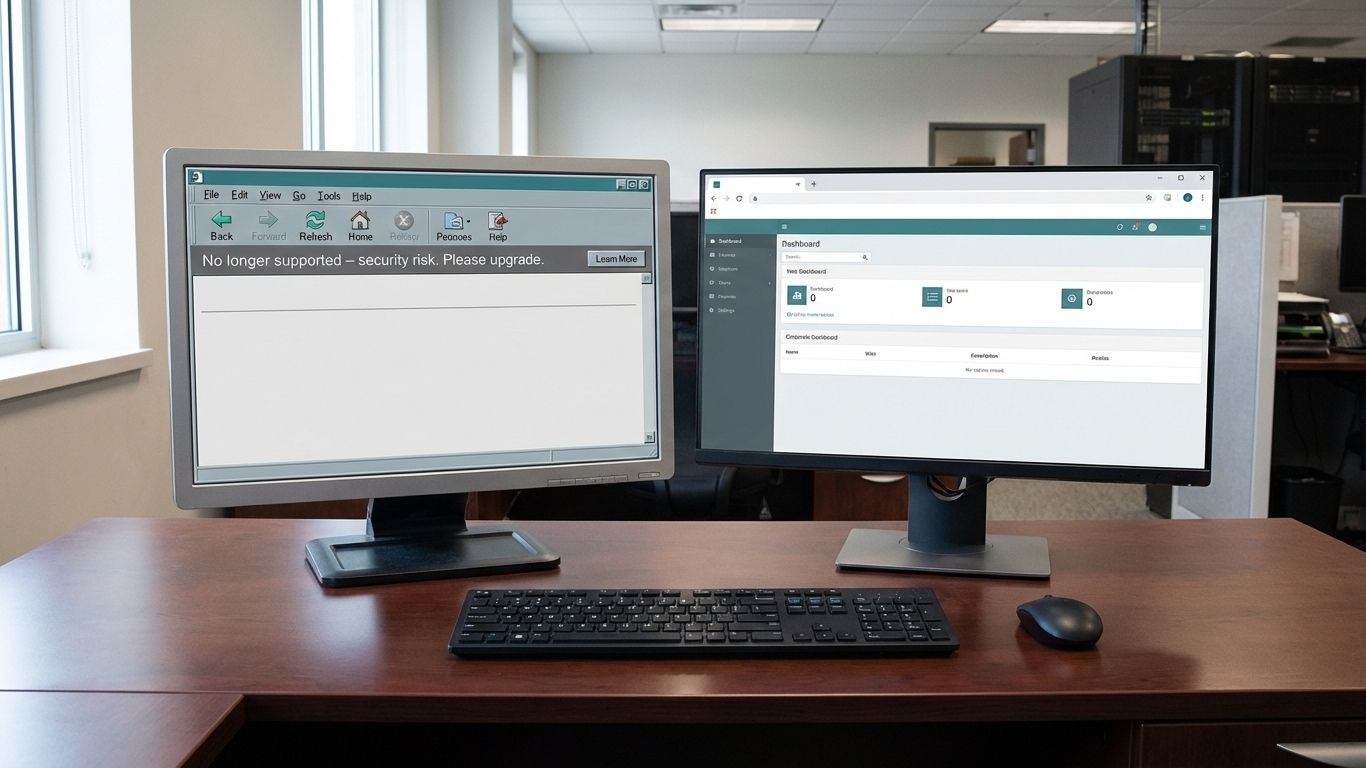
A product used by hundreds of millions of people became a legacy system not through failure, but through abandonment. For enterprises, this is the critical parallel: business-critical applications, however reliable today, become liabilities the moment their vendor stops supporting them. Legacy is about support and compatibility, not whether the system technically still runs.
The Real Costs and Risks of Holding On
Living with a legacy system may feel manageable in the short term. Over time, the costs compound in four distinct ways:
Security vulnerabilities
Systems without security updates become prime targets. Every known flaw remains permanently exploitable. According to IBM’s 2025 Cost of a Data Breach Report, the average cost of a data breach reached $4.35 million, and many breaches in healthcare and financial services trace back to unpatched legacy environments. In regulated industries, that exposure extends beyond recovery costs to include fines and reputational damage.
High maintenance costs
Expertise in COBOL, Visual Basic, and similar languages is increasingly scarce, which drives labour costs up sharply. Research suggests legacy maintenance can consume a significant portion of enterprise IT budgets, leaving little room for innovation or new capability development in some organisations.
Integration failures and data silos
Most legacy software systems were built before APIs and cloud infrastructure existed. Connecting them to modern analytics platforms, mobile applications, or cloud services requires custom middleware that is brittle and expensive to maintain. The result is isolated data: customer records, transaction histories, and operational data locked in systems that other departments simply cannot reach.
Performance bottlenecks
Legacy systems were designed for past volumes. When traffic spikes or data loads grow beyond their original parameters, they slow, fail, or produce errors. Real-time processing, mobile access, and modern AI integrations are often simply incompatible with the underlying architecture.
Modernisation or Replacement? Understanding Your Options
There is a persistent myth that organisations face a binary choice: complete replacement or indefinite delay. Neither is accurate. Legacy system modernisation exists on a spectrum, and most organisations have more options than they realise.
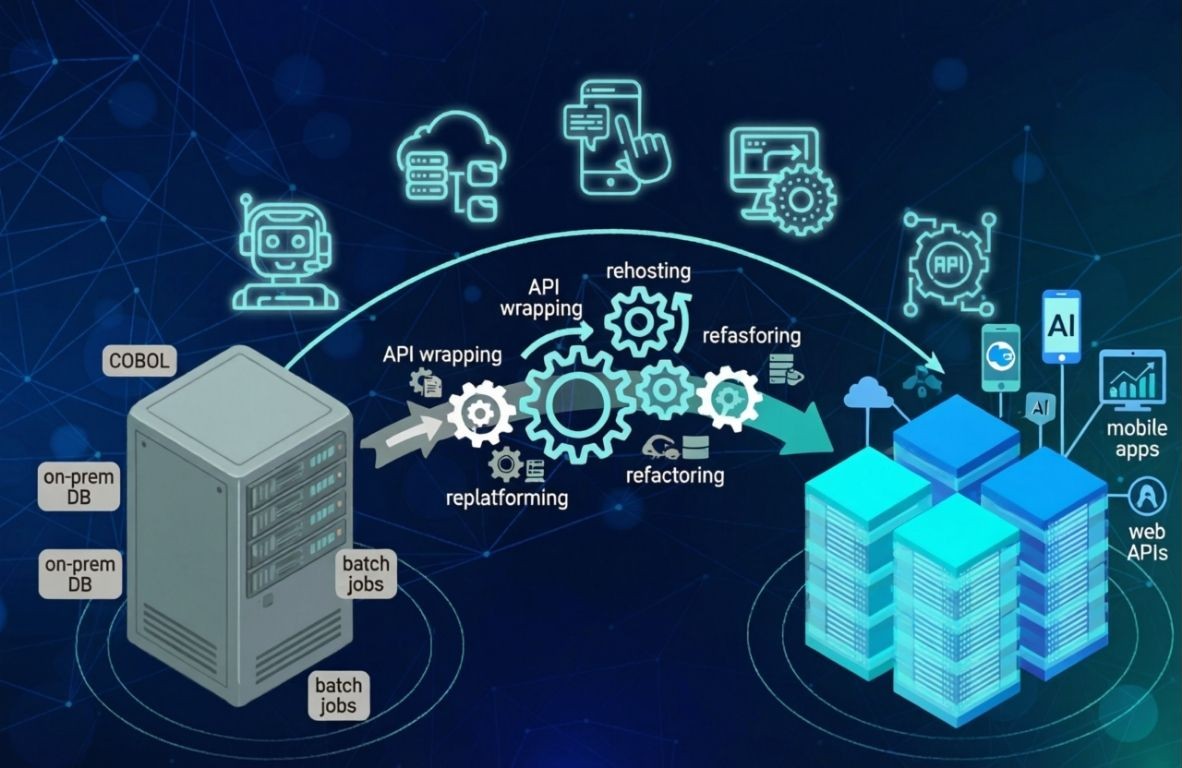
The right approach depends on risk tolerance, budget, operational complexity, and how deeply the legacy system is embedded in core processes. These are the five primary strategies:
- Encapsulation / API Wrapping. A modern interface layer is built around the existing application. The legacy core remains untouched internally, but new systems interact with it through APIs. New features are added in the outer layer over time, without touching the running core.
- Rehosting (Lift-and-Shift). The application moves as-is onto modern infrastructure, whether virtualised servers or the cloud, without changing any code or logic. This reduces hardware costs, extends the system’s operational life, and carries low risk since nothing functional changes.
- Replatforming. Part of the system migrates to a new platform with minimal adjustments. A legacy on-premises database might move to a managed cloud database, for instance, while the application logic remains intact. This delivers performance and scalability improvements without a full rebuild.
- Refactoring. The codebase is restructured and improved without altering what it does externally. This often follows a strangler-fig pattern, gradually transforming parts of the legacy system from within while its external behaviour remains unchanged for users and dependent systems.
- Full Replacement. A new modern system is built or purchased to replace the legacy platform entirely. This is the heaviest option, appropriate only when no other approach can meet the organisation’s security, compliance, or performance requirements. It is costly and disruptive, and it should be the last resort, not the default assumption.
Is replacing a legacy system worth it?
If a system is end-of-life, deeply insecure, or a structural barrier to digital goals, the case for full replacement strengthens considerably.
If the system still reliably handles core processes and the risk of a rewrite is prohibitive, pursuing encapsulation, rehosting, or refactoring can deliver comparable benefits at a fraction of the disruption.
Many enterprises find that a hybrid approach works best: wrap and stabilise the legacy system first, then refactor or replace components incrementally over a multi-year roadmap.
The goal is not to solve everything at once.
It is to keep the business running today while steadily building the architecture it will need tomorrow.
About HBLAB
Modernising a legacy system is one of the most consequential decisions an IT leader can make. Getting it wrong is costly. Getting it right requires a partner with the technical depth to navigate complexity and the process discipline to deliver without disruption.
HBLAB is a custom software development firm with over a decade of experience helping enterprises untangle outdated infrastructure and build systems fit for the future. With a team of 700+ IT professionals, 30% of whom carry five or more years of hands-on experience, HBLAB brings senior-level capability to every stage of the modernisation journey, from API wrapping and replatforming through to full system replacement.

For organisations balancing the cost of legacy maintenance against the risk of migration, HBLAB’s engagement model offers a practical advantage. Clients gain up to 30% cost efficiency compared to local development rates, without sacrificing quality. CMMI Level 3 certification underpins every project with rigorous process standards, enterprise-grade security safeguards, and full intellectual property protection, critical considerations when the systems being modernised sit at the heart of business operations.
HBLAB also offers flexible structures including dedicated teams, offshore delivery, and a Build-Operate-Transfer (BOT) model, giving organisations full control over workflows, tooling, and long-term ownership. Whether the goal is a phased modernisation or a clean migration, the engagement adapts to the complexity of the system and the pace the business can sustain.
CONTACT US FOR A FREE CONSULTATION
FAQ
1. What is a legacy system?
A legacy system is hardware or software that still performs essential business functions but is no longer actively supported, updated, or easily compatible with modern infrastructure. Examples include mainframes and terminals, on premises ERP or Windows XP era applications, and code written in older languages such as COBOL or Visual Basic 6.
2. Why are legacy systems still used?
Because they keep running critical work, replacing them is costly and risky, and much institutional knowledge and compliance logic is embedded in the old code. For many organizations, the short term risk of disruption outweighs the immediate benefit of replacement.
3. What are the problems with legacy systems?
They accumulate security vulnerabilities, require scarce maintenance skills, resist integration with modern APIs, create data silos, and cause performance and scalability bottlenecks. Over time these problems raise costs and slow innovation.
4. Why do banks use legacy systems?
Banks use them because decades of transaction processing, audit trails and regulatory controls were built on those platforms; regulators and operations trust their mature, proven behaviour. Rewriting core banking logic is complex, expensive and risky, so many banks modernize gradually rather than replace everything at once.
5. Is replacing a legacy system worth it?
It depends. Full replacement is worth it when a system is end of life, creates intolerable security or compliance risk, or blocks strategic goals. If the system still meets core needs, less disruptive modernization strategies such as API wrapping, rehosting or refactoring can be more cost effective.
6. How much does it cost to maintain a legacy system?
Costs vary widely. For small systems the annual maintenance can be tens of thousands of dollars. For large, enterprise critical systems maintenance and related operational overhead can run into millions or tens of millions per year, and some studies show legacy maintenance can consume a very large share of IT budgets. Use total cost of ownership modelling to compare continuing maintenance versus phased modernization.
7. What are the risks of legacy system security?
Unpatched code invites exploitation, data breaches and regulatory fines. Legacy systems often lack modern authentication, encryption and logging; they can be the weakest link that attackers use to pivot into critical networks. The longer updates are delayed, the larger and more expensive the breach consequences become.
READ MORE:


