Cybersecurity standards are documented specifications that define the requirements, controls, and best practices organisations must implement to protect their information systems and data from cyber threats. They provide a common language and measurable criteria for security practices, enabling businesses to demonstrate due diligence to regulators, customers, and partners.
When organisations adopt recognised standards, they gain a structured approach to risk management that would otherwise require years of internal development. Standards also facilitate trust between business partners, as they provide an independently verifiable benchmark for security posture.
Whether an organisation handles personal data, financial transactions, or critical infrastructure, the appropriate cybersecurity standards offer a roadmap for building resilience against increasingly sophisticated attacks.
What Is a Cybersecurity Framework?
A cybersecurity framework is a structured collection of guidelines, best practices, and processes that organisations use to manage and reduce their cybersecurity risks. It differs from a cybersecurity standard in both purpose and flexibility.
A standard is a formal, documented specification of requirements that an organisation must meet to achieve compliance or certification. A framework, by contrast, offers a broader, more adaptable structure of guidance that organisations can tailor to their specific circumstances.

Most frameworks share four core functions that form the foundation of effective security management:
- Risk assessment — identifying assets, threats, vulnerabilities, and the potential impact of security incidents
- Policy definition — establishing the rules and responsibilities that govern security behaviour
- Control implementation — the practical deployment of technical and administrative measures to mitigate identified risks
- Continuous monitoring — ensuring controls remain effective and that new risks are detected promptly
No single framework can serve every organisation because of the diversity of industries, jurisdictions, and data types involved.
A hospital handling patient health information faces different regulatory obligations than a software company processing credit card transactions.
A defence contractor working with classified government data operates under stricter requirements than a small e-commerce retailer.
Geographic location matters equally, since the European Union, United States, and Asia Pacific regions each have distinct legal frameworks governing data protection and security.
The most effective approach is to understand which cybersecurity standards apply to your organisation and then select a framework that aligns with those requirements while addressing your specific risk profile.
How Companies Keep Up with Evolving Cybersecurity Compliance Standards
The practical challenge of maintaining compliance grows more complex each year as regulations change, new threats emerge, and frameworks receive periodic updates. Organisations cannot treat compliance as a one-time exercise. They must develop systematic approaches to track, interpret, and implement changes to cybersecurity compliance standards on an ongoing basis.

Continuous monitoring and gap analysis form the foundation of effective compliance management. Organisations regularly audit their current controls against updated standards to identify areas where their security posture falls short. This process typically involves automated scanning tools, manual reviews of policies and procedures, and periodic assessments by external auditors. Gap analysis reveals not only where improvements are needed but also helps prioritise remediation efforts based on risk severity and regulatory deadlines.
Dedicated compliance roles provide the human expertise necessary to navigate the evolving regulatory landscape. The Chief Information Security Officer, commonly referred to as CISO, bears primary responsibility for tracking regulatory updates and ensuring the organisation responds appropriately. The CISO works with a compliance team that monitors regulatory announcements, participates in industry working groups, and maintains relationships with legal counsel specialising in cybersecurity regulation standards.
Mature organisations use a control mapping approach to satisfy multiple standards simultaneously rather than duplicating effort. Many cybersecurity standards share common control requirements — access management, encryption, and incident response, for example. By mapping controls across frameworks, a single set of measures can satisfy ISO 27001, NIST CSF, and industry-specific regulations at the same time, reducing the administrative burden significantly.
Vendor and supply chain compliance has become an essential component of most frameworks. Organisations increasingly rely on third-party services for critical functions, from cloud infrastructure to payment processing. A security breach at a vendor can expose the organisation and its customers just as directly as an internal breach. Modern cybersecurity compliance standards therefore require organisations to assess vendor security practices, include security requirements in contracts, and monitor vendor compliance over time.
Staff training and awareness addresses the human element of security, which remains the leading cause of security incidents despite advances in technical controls. Phishing attacks, social engineering, and poor password hygiene continue to breach organisations with otherwise strong security measures. Effective training programmes are built around the specific requirements of applicable standards, teaching employees not only what behaviours to avoid but why those behaviours matter for compliance.
How does a company know which framework is right for it? The decision involves several criteria evaluated together:
- Industry sector determines which regulations apply, such as HIPAA for healthcare or PCI DSS for payment processing
- Geographic jurisdiction affects which data protection laws apply, with GDPR covering any organisation processing EU residents’ data
- Data type — personal, financial, and health data each trigger specific regulatory requirements
- Market — companies in regulated sectors such as financial services or defence face additional obligations that may mandate specific frameworks
Selecting the right framework is comparable to choosing a building code: a residential contractor in California follows different structural requirements than a commercial developer in Germany, yet both work toward the same underlying goal of safety.
Top 5 Cybersecurity Standards and Frameworks

The following five frameworks represent the most widely adopted, internationally recognised, and frequently required cybersecurity standards in use today. Enterprise contracts, government procurement, and financial regulation commonly require or recognise each of them. Understanding their differences and relationships helps organisations build a compliance strategy that addresses multiple obligations efficiently.
1. ISO 27001 and ISO 27002
ISO 27001 is the internationally recognised standard for establishing, implementing, maintaining, and continually improving an Information Security Management System, commonly abbreviated as ISMS. An ISMS is a systematic approach to managing sensitive information so that it remains secure, encompassing people, processes, and IT systems through a risk management process. ISO 27001 specifies the requirements an organisation must meet but does not prescribe exactly how to meet them, which allows considerable flexibility in implementation.
ISO 27002 serves as the companion guide providing a detailed catalogue of security controls. The relationship between the two standards is direct: ISO 27001 tells you what to do; ISO 27002 shows you how to do it. The current version, ISO 27001:2022, reflects updates addressing cloud services, threat intelligence, and other modern security challenges.

The certification process involves a third-party audit conducted by an accredited certification body. Auditors assess whether the organisation has properly implemented the required elements of an ISMS and whether the system is effective. Certification is valid for three years, with annual surveillance audits confirming ongoing compliance. Organisations pursue ISO 27001 certification for contractual requirements from customers, regulatory recognition in certain sectors, and the credibility that comes from independent verification.
When comparing ISO 27001 vs NIST, the key distinction is this: ISO 27001 is a certifiable international standard with defined requirements, while NIST CSF is a voluntary, flexible guidance framework developed by a United States government agency. Both can be used together, and many organisations implement ISO 27001 for certification purposes while using NIST CSF for operational risk management.
2. ISO/IEC 27032:2023
ISO/IEC 27032 is a specialised standard focused specifically on cybersecurity in the context of the internet and connected environments. It distinguishes itself from ISO 27001 by addressing the unique challenges of interconnected digital ecosystems. The 2023 revision represents a significant update that reflects the evolution of cyber threats and the growing importance of collaborative security approaches.
The standard emphasises stakeholder coordination as a fundamental principle. An attack on one entity can cascade through supply chains, partner networks, and shared infrastructure. ISO/IEC 27032:2023 provides guidance for building coordinated defences against phishing, data breaches, and cyber sabotage. It is particularly relevant to cloud service providers, platform companies, and any organisation whose security depends on the security of others in their digital ecosystem.
Implementation of ISO 27032 complements rather than replaces ISO 27001. Organisations typically establish their ISMS under ISO 27001 and then apply ISO 27032 principles to address the additional complexities of internet security.
3. NIST Cybersecurity Framework 2.0
The NIST Cybersecurity Framework, commonly abbreviated as NIST CSF, was developed by the National Institute of Standards and Technology, a United States federal agency. Although originally designed for US critical infrastructure, the framework has achieved widespread global adoption due to its flexibility and practical utility.
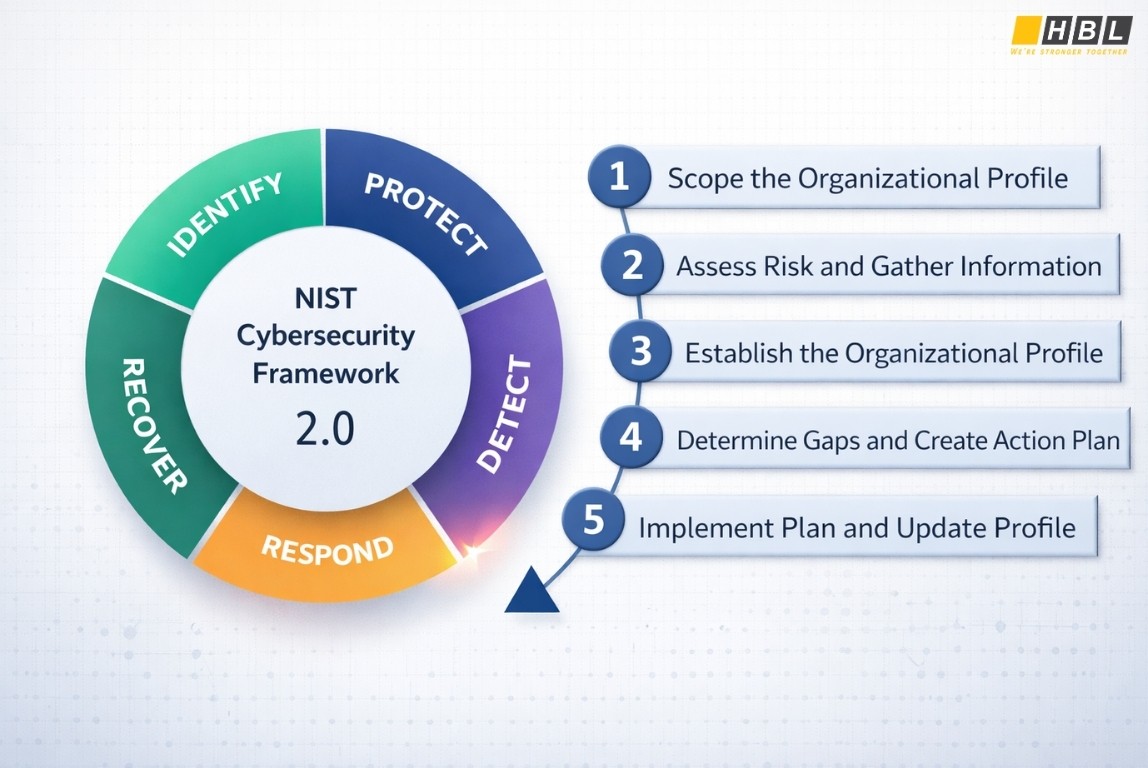
The five original core functions of the NIST CSF are:
- Identify — understanding organisational context, assets, and risks
- Protect — implementing safeguards to ensure delivery of critical services
- Detect — enabling timely discovery of cybersecurity events
- Respond — containing the impact of incidents
- Recover — restoring capabilities impaired by incidents
NIST CSF 2.0, published in February 2024, introduced a sixth core function: Govern. The Govern function addresses organisational-level accountability and risk management strategy, recognising that effective cybersecurity requires clear leadership, adequate resources, and alignment between security activities and business objectives. This addition reflects the understanding that cybersecurity is not merely a technical problem but an organisational governance challenge requiring executive oversight.
In practice, ISO 27001 and NIST CSF serve complementary purposes. ISO 27001 provides a certification pathway with defined requirements that auditors can assess objectively. NIST CSF offers flexible guidance that organisations can adapt to their risk appetite and maturity level.
4. GDPR Framework
GDPR, the General Data Protection Regulation, is not a cybersecurity standard in the traditional sense but a binding European Union regulation with direct cybersecurity implications. Any organisation that processes the personal data of EU residents must comply, regardless of where the organisation is based.
GDPR imposes several cybersecurity-specific obligations:
- Data protection by design and by default — security measures must be integrated into systems from the outset, not added later
- 72-hour breach notification — Article 33 mandates notification to supervisory authorities within 72 hours of becoming aware of a personal data breach
- Appropriate technical and organisational measures — the regulation requires security proportionate to the risk, though it does not prescribe specific controls
Implementing ISO 27001 substantially supports GDPR compliance because the standard’s controls address many of the security measures GDPR requires. However, ISO 27001 certification does not guarantee GDPR compliance, because the regulation includes additional requirements around data subject rights, lawful processing, and cross-border data transfers that fall outside the ISO standard’s scope.
Penalties for GDPR violations can reach €20 million or 4% of global annual turnover, whichever is higher — making it one of the most influential cybersecurity regulation standards globally.
>> GDPR’s Seven Data Protection Principles
5. Common Criteria (CC) / ISO/IEC 15408
Common Criteria, formally designated as ISO/IEC 15408, differs fundamentally from the other frameworks on this list. It is an international standard for evaluating and certifying the security properties of IT products, rather than organisational practices. A vendor of a firewall, operating system, or encryption module might seek Common Criteria certification to demonstrate independently verified security requirements.
The standard uses an Evaluation Assurance Level, abbreviated as EAL, as a seven-level scale rating the rigour of the evaluation process. EAL1 represents the lowest assurance level; EAL7 the highest, appropriate for extremely high-risk situations. Most commercial products achieve EAL2 through EAL4, with EAL4 being the highest level typically practical for general-purpose commercial products.
Government procurement bodies and defence agencies frequently require Common Criteria certification for products used in sensitive environments. The standard also enables mutual recognition of security evaluations across participating countries, reducing the need for duplicate testing when products are sold internationally.
Cybersecurity Standards for Fintech Companies
Fintech companies face a uniquely complex compliance landscape because they handle financial data, personal data, and payment data simultaneously. They operate across multiple jurisdictions and are subject to both financial regulation and cybersecurity regulation. Understanding which cybersecurity standards for fintech companies apply requires navigating an intersection of requirements that continues to evolve as regulators respond to innovations in financial technology.

ISO 27001 serves as the baseline for information security management in any organisation handling sensitive data. Financial institutions that partner with fintechs typically require evidence of robust security practices, and ISO 27001 certification provides that evidence in a recognised, verifiable form.
PCI DSS (Payment Card Industry Data Security Standard) applies to any organisation that processes, stores, or transmits cardholder data. Its 12 core requirements span six goals:
- Build and maintain a secure network
- Protect cardholder data
- Maintain a vulnerability management programme
- Implement strong access control measures
- Regularly monitor and test networks
- Maintain an information security policy
Non-compliance exposes companies to financial penalties and potential loss of card processing privileges.
DORA (Digital Operational Resilience Act) is the EU regulation specifically designed for financial entities, including fintechs. DORA requires organisations to manage ICT (Information and Communications Technology) risks systematically, test operational resilience regularly, and report major incidents to regulators. Effective January 2025, it represents the most comprehensive cybersecurity resilience requirement for European financial services to date. DORA also establishes an oversight framework for critical third-party ICT service providers, directly addressing supply chain risks.
GDPR applies to fintech data practices in multiple ways. KYC (Know Your Customer) data, transaction records, and behavioural profiling all involve personal data processed at scale, triggering comprehensive GDPR obligations around consent, purpose limitation, and data subject rights.
NIST CSF provides a risk management framework that fintechs operating in or with the US market frequently adopt. When working with US banking partners or seeking FedRAMP authorisation for cloud services, alignment with NIST CSF demonstrates security maturity to stakeholders.
The essential technical measures fintech companies must implement across these standards include:
- Encryption of data at rest and in transit throughout its lifecycle
- MFA (Multi-Factor Authentication) for all privileged access
- Secure API (Application Programming Interface) management and access control
- Continuous vulnerability scanning and penetration testing
- Incident response and business continuity planning
The practical challenge of multi-framework compliance drives fintech companies to adopt GRC (Governance, Risk, and Compliance) platforms. These tools map controls across frameworks simultaneously, demonstrating how a single technical measure satisfies requirements in ISO 27001, PCI DSS, GDPR, and DORA at the same time — reducing both cost and compliance complexity.
Frequently Asked Questions
1. What are some cybersecurity standards?
ISO 27001 is the international standard for information security management systems. NIST CSF provides a risk-based framework for managing cybersecurity. GDPR governs data protection for EU residents with significant security requirements. PCI DSS establishes requirements for organisations handling payment card data. Common Criteria (ISO/IEC 15408) certifies the security properties of IT products.
2. What are the current cybersecurity standards?
The most current versions are ISO 27001:2022, NIST CSF 2.0 (published February 2024), ISO 27032:2023, and DORA (effective January 2025) for EU financial entities. Organisations should verify they are working with the latest versions as standards undergo periodic revision.
3. What is the ISO standard for cybersecurity?
ISO 27001 is the primary ISO standard for cybersecurity, governing information security management systems. ISO 27032 addresses cybersecurity specifically in internet-connected environments. The two standards work together, with ISO 27001 providing the management system foundation and ISO 27032 offering additional guidance for interconnected security challenges.
4. What are the 5 standards of NIST?
The five original NIST CSF core functions are Identify, Protect, Detect, Respond, and Recover. NIST CSF 2.0, released in February 2024, added a sixth function — Govern — to address organisational accountability and risk management strategy at the executive level.
5. What is ISO 27001 vs NIST?
ISO 27001 is a certifiable international standard with defined requirements that organisations can be formally audited against. NIST CSF is a voluntary, flexible guidance framework developed by a US government agency. Both are compatible — many organisations use ISO 27001 for certification and customer assurance while applying NIST CSF for day-to-day risk management.
6. What are the 5 C’s of cybersecurity?
The five C’s are Change, Compliance, Cost, Continuity, and Coverage. Change addresses the need to adapt security measures as threats evolve. Compliance ensures alignment with regulatory requirements. Cost balances security investment against risk reduction. Continuity maintains operations during and after incidents. Coverage ensures security measures address all critical assets and risks.
READ MORE: